- Why International Digital Marketing Services Are Placing Increasing Importance on LocalizationApr 29 2026View details
- What are some practical Meta advertising tips to avoid common pitfalls?Apr 29 2026View details
- What should you do when search engine ranking algorithms change?Apr 28 2026View details
- What customer acquisition scenarios is GEO precision marketing suitable for?Apr 24 2026View details
- Which aspects should you optimize first in Facebook ad campaigns?Apr 24 2026View details
- What practical details are there for Meta ad placement?Apr 24 2026View details
- How can social media marketing strategies deliver more consistent results?Apr 24 2026View details
- Should rankings of internet marketing consulting firms be trusted?Apr 25 2026View details
How to Ensure Data Security in Foreign Trade Marketing Systems
Is foreign trade marketing system data secure? The answer is not a simple “secure” or “insecure”, but depends on whether the platform architecture, permission management, transmission encryption, backup mechanisms, and daily operation and maintenance are properly in place. For companies that rely on websites for customer acquisition, SEO optimization, advertising campaigns, and customer data accumulation, data security not only affects business continuity, but is also directly related to customer trust, inquiry conversion, and overseas compliance risks. This article will start from the practical issues companies care about most, break down how data security for foreign trade marketing systems is ensured, and what to focus on when selecting and implementing a solution.
First, identify the user's search intent: Users searching for “how to ensure data security for foreign trade marketing systems” mainly want to understand: whether the marketing system may leak customer information, website data, and business opportunity information; what measures companies should take to reduce risks such as attacks, data loss, operational errors, and compliance issues; and how to determine whether the security capabilities of an integrated website + marketing service platform are truly reliable when making a selection.
The issues target readers care about most: Business decision-makers care more about whether the system will affect business growth, brand reputation, and return on investment; operators are concerned about account permissions, recovery from accidental deletion, form lead protection, and daily usage security; while security management and after-sales maintenance personnel pay more attention to SSL certificates, access control, log auditing, backup and recovery, vulnerability remediation, and anomaly monitoring.
Therefore, this article focuses on: the core risk points of data security, truly effective protection mechanisms, platform selection criteria, and daily management actions; while generic statements such as “security is important” and “protection should be emphasized” will be minimized as much as possible, helping readers quickly form an actionable evaluation framework.
When it comes to data security in foreign trade marketing systems, what key points should companies look at first?
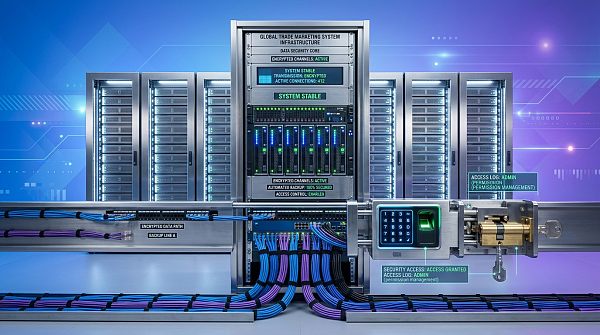
If a company is using or preparing to launch a foreign trade marketing system, it is recommended to first evaluate the security level from the following five aspects, rather than looking only at a single indicator such as “whether there is a firewall” or “whether there is encryption”.
1. Whether customer data is protected during both transmission and storage
Foreign trade marketing systems usually carry sensitive content such as inquiry forms, customer email addresses, phone numbers, chat records, order information, and visitor behavior data. If only the login page is encrypted, but form submission, backend interfaces, file downloads, and other links are not uniformly protected, there is still a risk of data exposure.
A mature platform should at least have:
- Site-wide HTTPS encrypted transmission to prevent data from being intercepted or tampered with during transmission
- A standardized SSL certificate application process and renewal mechanism before expiration to avoid browser blocking or reduced trust caused by certificate invalidation
- Encryption or masking of sensitive database fields to reduce the risk of internal data leakage
- Access control for static resources such as files, images, and attachments to prevent direct directory traversal and downloads
2. Whether account permissions are tiered, instead of “one administrator manages everything”
Many enterprise data leaks are not caused by hacker intrusions, but by excessive internal permissions, shared accounts, and failure to revoke permissions promptly after employees leave. Especially when foreign trade teams, customer service, channel partners, agents, and maintenance personnel all use the system at the same time, the risk will be amplified if there is no role separation.
A more reasonable approach is:
- Set role-based permissions according to job functions, such as granting separate permissions to marketing, sales, customer service, operations, and technical teams
- Restrict high-risk operations such as export, deletion, bulk modification, and viewing customer data
- Enable two-factor authentication for key accounts
- Deactivate accounts immediately after resignation, job transfer, or the end of outsourced cooperation
3. Whether it has backup and rapid recovery capabilities
Security is not only about “preventing intrusion”, but also about “whether quick recovery is possible when something goes wrong”. Once a foreign trade marketing system loses website content, SEO pages, inquiry leads, or customer data due to accidental deletion, system failure, or malicious attacks, subsequent customer acquisition will be directly affected.
Therefore, companies should focus on confirming:
- Whether there is an automatic backup mechanism, and how frequent the backups are
- Whether backups are stored offsite to avoid a single point of failure
- Whether recovery by site, database, or point in time is supported
- Whether the recovery process has a clear SLA and how long it takes to restore business operations
4. Whether abnormal behavior is continuously monitored
If a system is only deployed without monitoring, it is difficult to detect attacks, abnormal access, and malicious crawling at the earliest stage. For companies that rely on search engine optimization services and advertising traffic generation, abnormal traffic is often not only a marketing issue, but may also be a security issue.
For example, through website traffic monitoring tools, the following can be identified:
- Large volumes of visits from abnormal source IPs
- Malicious submissions to form interfaces
- A sharp surge in page requests within a short period of time
- Suspicious access patterns from specific countries or regions
- Abnormal fluctuations in bounce rate, dwell time, and conversion paths
These data can help both marketing optimization and security early warning.
5. Whether the platform has a continuous update and vulnerability remediation mechanism
Foreign trade websites and marketing systems often need to integrate multiple modules such as forms, online chat, CRM, ad tracking code, and social media plugins. If the underlying programs are not updated for a long time and plugin sources are complex, they can easily become entry points for vulnerabilities.
The value of a truly reliable integrated platform lies not only in “having many functions”, but also in its ability to continuously perform version maintenance, security patch updates, and compatibility optimization, thereby reducing the technical risks borne by the enterprise itself.
In which links do the most common data security risks for foreign trade enterprises usually occur?
Many companies believe that enabling HTTPS on their website is enough. But in reality, the data risks of foreign trade marketing systems usually come from the following high-frequency scenarios.
Inquiry forms and customer lead leakage
If inquiry forms do not have anti-spam, anti-injection, and anti-junk submission protection, attackers may exploit interface vulnerabilities to obtain, contaminate, or even destroy customer data. For companies that rely on their official website for customer acquisition, this will directly affect sales follow-up efficiency and lead quality.
Employee errors leading to data loss
For example, accidentally deleting product pages, overwriting customer tags, exporting data incorrectly and leaking it externally, or bulk modifying SEO page URLs. In many cases, business interruption is not caused by technical attacks, but by missing processes and permission management.
Hidden risks brought by third-party plugins and interfaces
Social media sharing plugins, analytics code, online customer service, maps, marketing automation tools, etc., although improving operational efficiency, may also bring risks of data leakage or malicious code injection into pages if their sources are unreliable or interface authorizations are too broad.
Weak passwords and shared accounts
Problems like “admin+123456” are not uncommon. When multiple departments share a backend account, logs become impossible to trace. Once abnormal operations occur, it is difficult to identify the responsible person or determine the source of the leak.
Lack of isolation between servers and deployment environments
If the official website, test environment, campaign pages, and admin backend are deployed chaotically, or even share the same set of high-privilege configurations, once one weak point is breached, the risk may spread to the entire business system.
How can you determine whether an integrated website + marketing service platform is truly secure and reliable?
When selecting a solution, companies should not look only at case studies, price, and page effects, but should also include security capabilities in the evaluation checklist. The following items are especially critical.
Check whether it has systematic security capabilities rather than scattered functions
Truly effective data security does not end with “buying a certificate” or “installing a plugin”, but forms a closed loop from website building, content management, traffic monitoring, and lead collection to later maintenance. For foreign trade enterprises, the longer the business chain involving websites, SEO, advertising, social media, and so on, the more a unified platform is needed to manage permissions, data, and risks.
Check whether it balances business efficiency and security control
Security should not come at the cost of severely sacrificing efficiency. A good platform should ensure data security while still allowing operations, sales, and maintenance personnel to work efficiently. For example, supporting role-based collaboration, operation logs, anomaly alerts, and recoverable version management is more in line with actual business needs than simply “restricting everything”.
Check whether the service provider has continuous service capabilities
Easimon Information Technology (Beijing) Co., Ltd., since its establishment in 2013, has provided full-chain digital marketing solutions around scenarios such as intelligent website building, SEO optimization, social media marketing, and advertising campaigns. For enterprises, the value of a service provider lies not only in the launch stage, but more in whether it can continuously provide version iteration, monitoring and maintenance, risk investigation, and localization support afterward. Especially in overseas promotion scenarios, system stability and security maintenance capabilities often directly affect inquiry conversion and brand reputation.
Check whether it supports both brand presentation and secure operations
Some companies worry when upgrading their marketing systems: after emphasizing security, will front-end presentation effects and conversion experience be sacrificed? In fact, the two do not conflict. For example, the Fragrance, Personal Care, and Beauty solution for fragrance and lifestyle enterprises can build a professional and premium online portal while also balancing visual expression, customer communication efficiency, and business conversion through modular layouts, clear hierarchical structures, and fully responsive interaction. This also shows that the real standard of a mature integrated platform is being able to satisfy both brand marketing and underlying operational security.
When implementing data security protection, what is the most practical execution checklist for enterprises?
If enterprises hope to turn “data security” from a slogan into executable actions, they can prioritize implementing the following checklist:
- Enable HTTPS comprehensively for the official website, form pages, backend, and API interfaces
- Establish standardized SSL certificate application procedures, renewal reminders, and replacement mechanisms
- Classify and manage customer information, inquiry data, and order materials
- Set job-based permissions and prohibit unrelated personnel from viewing or exporting sensitive information
- Enable strong passwords and two-factor authentication for core accounts
- Deploy website traffic monitoring tools to monitor abnormal access, attack traffic, and form risks
- Regularly check server, CMS, plugin, and interface versions, and update patches promptly
- Establish automatic backup and recovery drill mechanisms instead of just “backing up without verification”
- Provide basic security training to employees, agents, and distributors to reduce human error
- Retain log audit records to ensure issues can be traced and reviewed after they occur
For managers, the significance of this checklist is that it can not only reduce the risk of data leakage and business interruption, but also avoid system problems dragging down SEO rankings, advertising performance, and customer follow-up efficiency. For execution teams, most of these actions can be incorporated into daily operation and maintenance processes and are highly practical.
If data security is done well, what practical value does it bring to foreign trade business growth?
Many companies regard data security as a cost item, but from the perspective of foreign trade marketing practice, it actually directly affects the quality of growth.
Improve customer trust and conversion rates
When customers visit the official website, browser security indicators, stable page loading, and a trustworthy form submission experience all affect whether they are willing to leave their contact information. This is especially true for overseas B-end customers, who are usually more sensitive to the professionalism and security of a corporate website.
Reduce lead loss and after-sales costs
If customer information is missed due to unstable systems, invalid forms, or data loss, the enterprise will not only lose current inquiries, but also increase subsequent remediation and customer explanation costs.
Protect SEO and advertising performance
Problems such as website tampering, abnormal redirects, slower loading speed, and certificate expiration can all affect search engine crawling and user experience, thereby impacting organic rankings and landing page performance for ads. Security and marketing are actually issues on the same chain.
Lay the foundation for long-term brand operations
The more a company values global growth, the less it can focus only on short-term traffic. A stable, secure, and sustainably operated marketing system is the foundation for a brand’s long-term accumulation of content assets, customer assets, and channel assets.
Overall, the key to how data security for foreign trade marketing systems is ensured does not lie in a single technical term, but in whether a complete mechanism has been established covering transmission encryption, permission management, backup and recovery, anomaly monitoring, vulnerability remediation, and daily operation and maintenance. For enterprises, when judging whether a platform is reliable, do not look only at functions and price, but also at whether it can truly protect customer data, website assets, and brand reputation while ensuring growth efficiency. Only by making security part of the marketing system, rather than an after-the-fact remedy, can a company’s global customer acquisition and long-term operations become more stable.
Related Articles
Related Products