- What should you look for in recommended digital marketing strategy agencies? Bigger names are not always the better fitMay 05 2026View details
- Your Facebook ad strategy keeps missing the mark? Avoid these three audience types firstMay 05 2026View details
- Is It Still Necessary to Build a Multilingual Marketing System in 2026?May 04 2026View details
- How to Evaluate the Performance of AI Smart Advertising Platform Campaigns in 2026?May 04 2026View details
- How to Choose the Most Cost-Effective Global CDN Acceleration in 2026?May 04 2026View details
- How to choose social media operations training? Focus on hands-on practice or case studiesMay 04 2026View details
- Digital marketing SaaS solutions: build in-house or outsourceMay 04 2026View details
- How to read an enterprise services SaaS report? Key points for vendor selectionMay 04 2026View details
Is foreign trade marketing system data secure? Ask these questions before choosing one
Is data in foreign trade marketing systems secure? Before choosing a foreign trade B2B website development service provider, companies should clearly ask about permissions, backups, compliance, and the SSL certificate application process to avoid obstacles to later maintenance and growth.
Why data security in foreign trade marketing systems cannot be judged only by whether it “works”

For foreign trade companies, a marketing system is no longer just a simple website backend, but a central hub for websites, inquiries, social media, advertising, and customer data. Once permissions are disorganized, backups are missing, or certificate management is not properly handled, the impact is often not limited to 1 page, but can affect customer acquisition, follow-up, and conversion efficiency for several consecutive weeks.
What users worry about most is complicated operation and difficulty recovering from accidental deletion; project owners worry that no one will take over after delivery; business decision-makers are more concerned about 3 types of risks: customer data leakage, unstable overseas access, and restrictions on ongoing fees and migration. These issues are especially common in integrated website + marketing service projects.
Many companies only compare price and homepage design in the early stage, while overlooking the underlying system rules. What truly determines long-term security usually includes 4 basic areas: account permissions, data backup, transmission encryption, and compliance governance. Failing to ask one more question early on may cost an extra 2–4 weeks of remediation later.
Yiyingbao Information Technology (Beijing) Co., Ltd. has been deeply engaged in global digital marketing services for more than 10 years, building end-to-end capabilities around intelligent website development, SEO optimization, social media marketing, and advertising placement. For companies preparing to go global, system security is not an isolated issue, but the prerequisite for whether the growth system can be sustained.
First clarify: what types of data are you actually protecting
A foreign trade marketing system usually involves at least 4 types of core data, and different types require different protection priorities. If a provider only vaguely promises “security and stability,” it often indicates that its solution is not detailed enough.
- Website asset data: including page content, product materials, form configurations, multilingual versions, and SEO settings, with the focus on recovery from accidental deletion, version retention, and migration convenience.
- Customer interaction data: including inquiry records, email leads, chat conversations, and source tags, with the focus on access permissions, audit trails, and export capabilities.
- Account connection data: including social media authorizations, advertising account bindings, and API synchronization status, with the focus on authorization validity periods, unbinding mechanisms, and exception alerts.
- Operational analytics data: including traffic sources, conversion paths, and campaign performance, with the focus on cross-departmental sharing boundaries and unified reporting standards.
If a company operates its official website, social media, and advertising at the same time, it is recommended to map out the data flow at the beginning of the project and use 1 checklist to specify “who can view, who can edit, and who can export,” which is far more efficient than troubleshooting afterward.
5 key questions to ask before selection that directly affect later maintenance costs
The following 5 questions are suitable for procurement, operations, and project owners to confirm directly with service providers during the comparison stage. They are related not only to security, but also to maintenance efficiency and controllability over the next 1–3 years.
Question 1: Are permissions divided by account, role, or functional module
A usable foreign trade marketing system should at least support role-based hierarchy, rather than having everyone share a super administrator account. Common roles can be divided into 5 categories: operations, editors, sales, management, and outsourced collaborators. The clearer the roles, the lower the risk of operational errors and internal risks.
If distributors, agents, or overseas teams also need access to the system, you should also confirm whether authorization can be granted by site, by language site, or by function menu. Otherwise, one content modification may affect pages in multiple markets.
Question 2: How are backup frequency, recovery method, and recovery time defined
Companies should at least clarify 3 points: whether backups are automatic, how long backups are retained, and whether recovery requires additional charges. A common practice is daily backup with retention for 7 days, 15 days, or 30 days, but there are significant differences among service providers, so this must be written into the delivery scope.
If the system is responsible for inquiry conversion tasks, you should further confirm whether the recovery target is the entire site, the database, or a single page. The finer the recovery granularity, the more downtime impact and manual rework can be reduced.
Question 3: Who applies for the SSL certificate, who renews it, and who handles certificate exceptions
Many companies think that if a website can be opened, it means it is secure, but that is not necessarily true. An SSL certificate is related not only to browser trust, but also affects form submission, search engine crawling, and the access experience of overseas users. If a certificate expires without renewal, it may cause warning prompts in minor cases, or directly affect inquiry conversion in serious cases.
Before signing a contract, 4 points should be clarified: the applicant entity, deployment responsibility, renewal reminders, and response time for exception handling. Under normal circumstances, certificate deployment and validation can usually be completed within 1–3 working days, provided the process is clear and responsibilities are well defined.
Question 4: Can the data be exported, and is migration restricted
A truly mature service will not rely on “data lock-in” to retain customers. Companies should require confirmation of whether website content, form data, inquiry records, media assets, and basic reports can be exported, and whether the export format is convenient for migration and secondary analysis.
Question 5: Does it cover compliance requirements and operation logs
If the business targets Europe, North America, or multiple regional markets, compliance is not only a legal issue, but also a threshold for cooperation. At a minimum, you should confirm whether basic capabilities such as privacy policy configuration, Cookie notices, form authorization, log retention, and account password management are in place.
To facilitate quick comparison during the procurement stage, it is recommended to organize the key questions into an evaluation table. The table below is suitable for direct use when comparing 2–3 service providers.
The value of this table lies not in the scoring itself, but in helping companies turn vague promises into executable terms. This is especially important for projects with tight delivery schedules and many collaborating departments, where boundaries need to be clarified before the contract is signed.
Compliance, encryption, and certification: what foreign trade companies should understand
Data security is not only about whether there is “protection,” but also whether that protection covers these 5 stages: collection, transmission, storage, invocation, and deletion. For websites and marketing systems targeting overseas markets, the earlier compliance design is introduced, the lower the later rectification cost.
From transmission to storage, check at least these 4 items
- Transmission encryption: whether website login, form submission, and API calls are completed through encrypted connections to avoid interception in transit.
- Sensitive data storage: whether information such as customer contact details and account tokens is stored in encrypted form rather than in plain text.
- Access control: whether different positions can only view the information required for their work, avoiding large-scale exposure of customer data.
- Log auditing: whether key operations are traceable for reviewing exceptions within 7 days, 15 days, or longer periods.
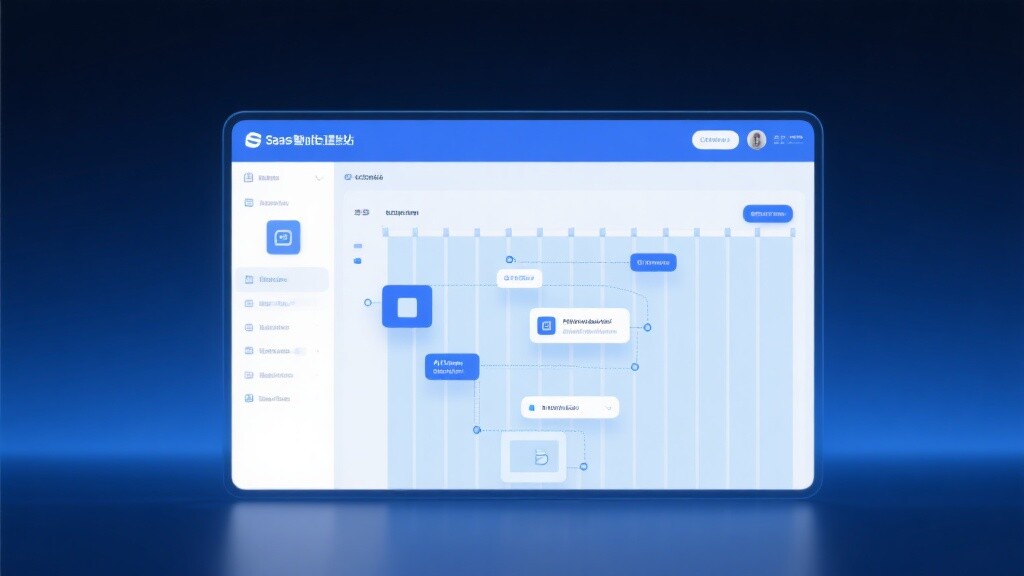
If a company operates both its official website and social media in tandem, authorization security is especially critical. Taking AI+SNS Social Media All-in-One Smart Marketing System as an example, it uses the OAuth2.0 protocol, encrypts and stores sensitive data, and complies with GDPR standards. Capabilities like these have more practical value in multi-platform collaboration scenarios.
For decision-makers, understanding certifications is not difficult. Certification is not “the more the better,” but should match the business scenario. For example, whether information security management covers organizational processes and whether personal data processing takes into account overseas market requirements are both more important than pure promotion.
Comparison of common compliance focus points
The table below can help companies quickly determine, in integrated projects involving website development, social media, and inquiry management, which capabilities are “must-haves” and which are “nice-to-have bonuses.”
If a service provider has passed ISO27001 information security certification and can demonstrate specific mechanisms such as encryption, authorization, and auditing in actual products, it usually indicates that its security development is closer to a truly implementable state rather than remaining at the level of verbal promises.
In integrated website + marketing service projects, which pitfalls are most easily overlooked during implementation
Many problems are not invisible during procurement, but are simply not watched during implementation. Especially within a 2–6 week launch cycle, website building, content, domain names, certificates, social media, and conversion tracking are often handled separately by different roles, and even a slight disconnect can leave hidden risks.
Common misunderstanding 1: launch first, then patch security settings later
This approach may seem to save time in the short term, but it actually leads to repeated rework. For example, publishing pages first and then adding SSL certificates and form rules can easily cause crawling fluctuations, failed form tests, or inconsistent data collection standards.
Common misunderstanding 2: social media, website, and customer service data are isolated from each other
Foreign trade companies are placing increasing importance on content collaboration. If official website articles, Facebook posts, LinkedIn content, and customer service leads are all scattered separately, the team not only repeats work, but also finds it difficult to form a unified customer profile. This is when the value of an integrated system truly becomes evident.
For example, tools that support multi-platform account binding, automatic content adaptation, and one-click synchronization can reduce the operational cost of switching back and forth across multiple platforms. For the overseas market expansion stage, this is often more stable than single-point tools and more conducive to long-term management.
Recommended 4-step implementation checklist method
- Step 1 confirm asset ownership: the responsible entity for domain names, certificates, servers, administrator accounts, and social media authorizations should be clearly assigned to the company or designated person in charge.
- Step 2 complete the security checklist: at a minimum, verify whether 6 items have been configured properly: permissions, backups, forms, logs, exports, and certificates.
- Step 3 conduct integration testing: carry out 1–2 rounds of complete testing for official website inquiries, social media synchronization, automated replies, and lead flow.
- Step 4 arrange delivery training: provide separate training for operators and management, and it is recommended to control it within 2 types of training scenarios to avoid “can understand but cannot use.”
If the company also plans to carry out coordinated social media operations, it can further evaluate solutions such as the AI+SNS Social Media All-in-One Smart Marketing System. It supports account binding for platforms such as Facebook, LinkedIn, Instagram, and Youtube, enabling independent site content to be extended more smoothly across multiple touchpoints.
For distributors, agents, and regional teams, this collaborative approach also has one direct value: it can maintain consistent brand content while reducing version deviations caused by repeated local team editing.
How to determine whether a service provider is truly suitable for long-term cooperation
A foreign trade marketing system is not the end once purchased, but accompanies at least 1 year or more of a company’s content operations, inquiry management, and overseas growth. Therefore, when making a selection, companies should distinguish between “delivery capability” and “long-term service capability.”
See whether the team understands both technology and marketing execution
If a team only understands website building but not customer acquisition, it is easy to turn the system into a display tool; if it only understands advertising placement but not underlying asset management, it will lead to chaotic maintenance later. Integrated website + marketing service projects require a closed loop from website building, SEO, and social media to advertising, rather than disconnection between each link.
Since its establishment in 2013, Yiyingbao Information Technology (Beijing) Co., Ltd. has used artificial intelligence and big data as its core driving force and has served more than 100,000 companies in achieving global growth. For companies that value efficiency, compliance, and sustainable operations, this kind of end-to-end capability is closer to actual needs.
See whether it can support expansion after delivery instead of only completing the current pages
What a company needs today may be an official website, but 3 months later it may add multilingual sites, a social media matrix, advertising landing pages, and automated customer service. If the system architecture and service process have no room for expansion, each additional module later may require rebuilding from scratch.
A more reliable criterion is whether phased implementation is supported. For example, first complete the official website and inquiry collection, then in phase 2 connect social media synchronization and customer profiling, and in phase 3 add intelligent customer service and conversion optimization. This is more conducive to budget control and also better suited to the internal collaboration rhythm of B2B companies.
Why choose us
If you are evaluating the data security of a foreign trade marketing system, the reliability of a foreign trade B2B website development service provider, or need to unify the planning of your official website, SEO, social media, and advertising, we can provide more specific support based on your actual business rather than simply giving a standard quotation.
- Parameter confirmation: help clarify permission hierarchies, backup frequency, log retention, and the division of responsibility for SSL certificate application and renewal.
- Product selection: based on company size, overseas market coverage, and team collaboration methods, determine whether a standalone site solution or an integrated marketing system is more suitable.
- Delivery schedule: based on the common 2–6 week implementation rhythm, evaluate the actual timeline for website building, migration, training, integration, and launch.
- Customized solutions: design more suitable processes for distributors, multilingual sites, overseas social media matrices, and customer service transfer scenarios.
- Certification and compliance: assist in clarifying GDPR-related requirements, ISO27001 focus points, and basic configuration checklists for overseas markets.
- Quotation communication: provide clearer budget recommendations based on functional scope, implementation depth, and follow-up service model to reduce hidden costs.
Before truly starting the project, clarifying data security, permission boundaries, backup strategies, and certificate processes is often more cost-effective than making corrections later. For companies preparing for long-term overseas growth, this is a necessary upfront investment and also a key step in reducing risk and improving conversion efficiency.
Related Articles
![Explosive foreign trade orders! Yiyingbao AI scheduled content generation + precise customer acquisition on FB, fully automated operations mode activated! Explosive foreign trade orders! Yiyingbao AI scheduled content generation + precise customer acquisition on FB, fully automated operations mode activated!]() Explosive foreign trade orders! Yiyingbao AI scheduled content generation + precise customer acquisition on FB, fully automated operations mode activated!
Explosive foreign trade orders! Yiyingbao AI scheduled content generation + precise customer acquisition on FB, fully automated operations mode activated!![Foreign trade promotion is full of pitfalls—don’t let your hard-earned money become tuition fees paid to “amateurs” Foreign trade promotion is full of pitfalls—don’t let your hard-earned money become tuition fees paid to “amateurs”]() Foreign trade promotion is full of pitfalls—don’t let your hard-earned money become tuition fees paid to “amateurs”
Foreign trade promotion is full of pitfalls—don’t let your hard-earned money become tuition fees paid to “amateurs”![Promote on Facebook with a personal account? You can't even target the right audience! Promote on Facebook with a personal account? You can't even target the right audience!]() Promote on Facebook with a personal account? You can't even target the right audience!
Promote on Facebook with a personal account? You can't even target the right audience!
Related Products