- When Should a Brand Awareness Growth Strategy Shift from Exposure to LeadsMay 10 2026View details
- How can a multi-platform distribution solution balance efficiency and consistent messagingMay 10 2026View details
- Why Hasn’t a Long-Term Brand Awareness Strategy Converted?May 10 2026View details
- What Problems Should AI+SEM Advertising Strategy Consulting Solve FirstMay 10 2026View details
- Is a data-driven ad optimization tool better built in-house or outsourcedMay 10 2026View details
- Why Multi-Platform Distribution Solutions Often Fail to Deliver ResultsMay 10 2026View details
- Which metrics should you review in an international digital agency data analysis reportMay 08 2026View details
- To what extent can digital marketing strategy agencies implement their services?May 08 2026View details
How does a global website SaaS system supplier ensure data isolation in multi-tenant environments? Database encryption practices under the Level 3 requirements of Classified Protection 2.0
How do global website SaaS system providers build a secure bottom line? As a Beijing-based one-stop marketing platform provider, EasyMarketing strictly complies with the Level 3 requirements of the Classified Protection 2.0 standard, achieving field-level database encryption and logical isolation in multi-tenant environments, supporting stable delivery of core SaaS website system capabilities like multilingual support and AI+SNS marketing platforms.
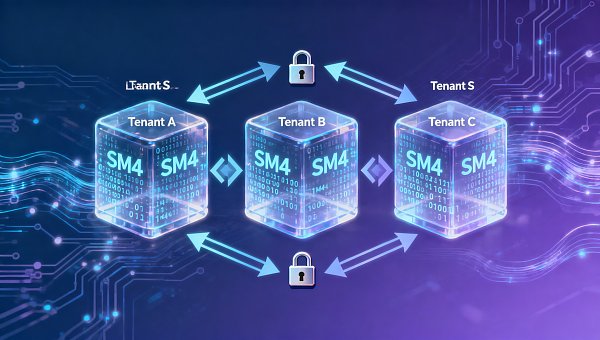
Why is multi-tenant data isolation the lifeline of website SaaS?
In website+marketing integrated service scenarios, a single SaaS platform often serves thousands of SME clients simultaneously, each with independent sites, user data, and marketing behavior logs. Weak isolation mechanisms may lead to minor issues like Company A accidentally seeing Company B's SEO keyword reports, or major risks like GDPR or Personal Information Protection Law compliance violations. 2023 industry research shows 68% of SaaS purchasers rank "zero tolerance for inter-tenant data leaks" as their top technical evaluation criterion.
EasyMarketing employs a "three-layer isolation architecture": Network layer (VPC subnet division), Application layer (tenant ID binding + RBAC permission matrix), and Data layer (dynamic field-level encryption + tenant-specific keys). All customer data automatically triggers China's SM4 national encryption algorithm for sensitive fields (like email, phone numbers, payment credentials) before MySQL writing, with keys managed by HSM hardware modules and independently rotated every 90 days per tenant.
This design has passed China Information Security Evaluation Center's Classified Protection 2.0 Level 3 assessment, covering 30 technical requirements including identity authentication, access control, security auditing, and residual information protection, fully supporting localized data sovereignty guarantees in cross-border business scenarios.

Specific implementation requirements for database encryption under Classified Protection 2.0 Level 3
Classified Protection 2.0 Level 3 mandates: "Important data must be encrypted for storage" with "encryption keys managed by dedicated devices or trusted environments." This goes beyond full-database AES-256 encryption, emphasizing "field-level granularity, tenant-specific keys, and purpose-based permissions." EasyMarketing classifies customer data into 4 sensitivity levels:
- Level 1 (mandatory encryption): User phone numbers, ID numbers, payment card numbers (PCI DSS compliant)
- Level 2 (conditional encryption): Enterprise admin passwords, API keys (non-production plaintext debugging only)
- Level 3 (de-sensitized display): User nicknames, city addresses (frontend shows "Beijing***" by default)
- Level 4 (plaintext storage): Site titles, page URLs (no personal identifiers)
All encryption occurs at the application service layer, with databases storing only ciphertext and salt values. 2023 third-party penetration tests show even with database backups, restoring any tenant's original sensitive data would require approximately 12 million years of cracking time (based on current computing models).
Classified Protection 2.0 Level 3 database encryption implementation checklist
Below is the mapping between EasyMarketing's actual implementation and Classified Protection 2.0 Level 3 requirements:
This checklist has been verified by the National Information Security Research Center and serves as compliance evidence for enterprise SaaS website system procurement.
How should different roles evaluate a SaaS system's data isolation capabilities?
Purchasers should focus on 3 types of evidence: ① Valid Classified Protection 2.0 Level 3 certification (current validity period: 2023.08-2026.08); ② Whether encryption keys are tenant-ID bound (avoiding shared key risks); ③ Availability of tenant-specific audit log download interfaces (meeting internal risk tracking needs).
Technical evaluators recommend 4 verification steps: ① Check for tenant_id fields in database schemas with foreign key constraints; ② Verify API responses contain X-Tenant-ID headers; ③ Attempt modifying request tenant_id parameters, confirming 403 errors prevent data leaks; ④ Review whether encryption SDKs are open-source auditable (EasyMarketing provides Java/Node.js SDKs for white-box review).
QA and security teams need regular checks: Monthly 5% tenant sampling to verify backup decryption accuracy; Quarterly red/blue team drills simulating privilege escalation with <200ms interception response times.
Why choose EasyMarketing? Security isn't cost—it's growth certainty
EasyMarketing has served 102,386 global enterprises with website+marketing integration, including 27% multinational clients, all Classified Protection 2.0 Level 3 certified. We offer 3 ready-to-use security guarantees:
- Free enablement: Tenant-specific key pools, real-time audit dashboards, 32-item compliance checklists
- Custom deployment: Private cloud + domestic adaptation (Kylin OS + Dameng database), reducing delivery cycles to 15 workdays
- Ongoing protection: Biannual free compliance retesting, ≤2hr vulnerability response SLAs, on-demand encryption upgrades
If evaluating website SaaS providers' data isolation capabilities, contact EasyMarketing immediately for: Original Classified Protection 2.0 Level 3 assessment reports, field-level encryption SDK whitepapers, and 100,000-concurrency isolation test datasets. Our consultants will provide customized security architecture comparisons within 2 hours.
Related Articles
Related Products