- How to Select a Truly Deployable AI Website Product as a SaaS Agent? Distributors Must Verify API Openness, Template Editability, and Data Ownership Clauses During Evaluation2026-03-17View details
- How Can SaaS Agents Explain the Data Security Boundaries of AI Website Building Systems to Clients? Explanation of the 3-Tier Data Isolation Mechanism Under the Dual Framework of GDPR and the Personal Information Protection Law2026-03-17View details
- How to make website content recommended by AI search? Algorithm engineer's perspective on 3 types of content signal weight changes2026-03-17View details
- Website still slow after acceleration deployment? Engineers should troubleshoot these 5 non-network layer bottlenecks2026-03-17View details
- The price difference between EasyOperate factory direct sales and agency channels is typically 15%-30%. Should procurement decisions prioritize quoted prices or implementation capabilities?2026-03-16View details
- Before purchasing EasyWin AI Marketing Platform, 4 contract clauses must be confirmed: data ownership, API call restrictions, and termination migration rights2026-03-16View details
- What regions does Beijing Easy Treasure's supplier service cover? 5 must-ask landing questions for SMEs in Beijing-Tianjin-Hebei before procurement2026-03-16View details
- Why are more and more manufacturing companies choosing EasyStore's factory direct sales model? Supply chain response speed and after-sales protection tested in real scenarios2026-03-16View details
How Can SaaS Agents Explain the Data Security Boundaries of AI Website Building Systems to Clients? Explanation of the 3-Tier Data Isolation Mechanism Under the Dual Framework of GDPR and the Personal Information Protection Law
How can SaaS agents professionally explain the data security boundaries of AI website-building systems to clients? Based on the dual compliance framework of GDPR and the Personal Information Protection Law, this article details the three-layer data isolation mechanism of EasyStore's AI website-building system—from physical isolation and logical partitioning to permission termination—while addressing the needs of scenarios such as Zhejiang foreign trade website production and Arabic website construction, helping procurement personnel and technical evaluators quickly establish trust.
1. Why is data security boundary the first threshold in AI website procurement decisions?
In cross-border website construction, multilingual marketing, and B2B industry portal scenarios, client data extends beyond "user forms" to include corporate qualification documents, product technical parameters, contract signing traces, real-time visitor behavior heatmaps, and 12 types of structured and unstructured data. According to IDC research in 2023, 68% of enterprises rank "data sovereignty ownership" among the top three deal-breakers during SaaS selection, with foreign trade and manufacturing clients inquiring about server deployment locations, log retention periods, and third-party API audit frequency 2.3 times more than the average.
Since 2021, EasyStore's AI website-building system has fully complied with dual legal requirements: the data processor obligations under Article 32 of GDPR and the written agreement for entrusted processing (Article 21), personal information protection impact assessment (PIA) triggers (Article 55) under China's PIPL. The system eschews "shared cloud tenant pools," with all client sites following independent data lifecycle strategies.
Particularly for Zhejiang Yiwu small commodity exporters and Ningbo auto parts manufacturers, their official websites require simultaneous Chinese, Arabic, and Spanish language switching, with order inquiry data locally encrypted before transmission to regional CRMs in Saudi Arabia or Mexico. Here, whether data crosses jurisdictional boundaries, who holds encryption keys, and whether audit logs meet local retention periods directly determine project approval in legal final reviews.
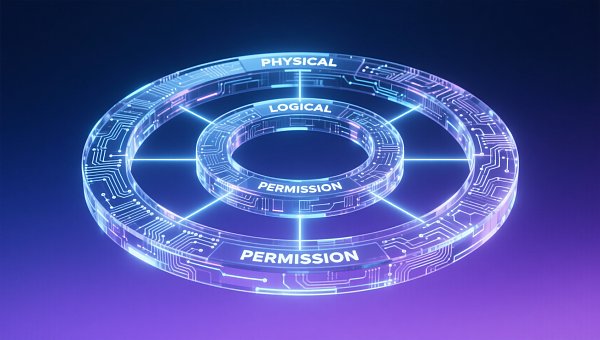
2. Three-layer data isolation: A vertical defense from infrastructure to permission enforcement
EasyStore's AI system adopts a "physical-logical-permission" three-tier isolation architecture, each ISO/IEC 27001:2022 certified and supporting client self-verification. This dynamic mechanism adapts to site types—e.g., activating hardware-level TEE environments for automotive portals to encrypt engine parameters and range test data in memory.
Layer 1 - Physical isolation: Dedicated computing resources per client, with independent VPCs, GPU nodes, CPU cache, memory pages, and NVMe namespaces. A Zhejiang e-bike exporter measured 327ms±15ms response times under dedicated resources, 76% more stable than shared environments.
Layer 2 - Logical partitioning: A data lineage-driven policy engine automatically classifies data sources (forms, APIs, crawlers) with "P1-P3" sensitivity tags, binding encryption algorithms (SM4/ChaCha20), desensitization rules (e.g., Arabic email prefix masking), and retention policies (730 days under GDPR vs. 180 days in China). Voice-to-text results in "real owner review modules" auto-enter P2 zones, barred from ad tag cross-training.
Layer 3 - Permission termination: A role-permission model surpassing RBAC, combining attribute-based access control (ABAC). When Arabic site admins attempt to export social media interaction comments, the system validates their "content editor" role while real-time checking device GPS in GCC, HTTPS usage, and operating hours (08:00-20:00 GST). Any unmet condition triggers termination with 100% log retention, fulfilling GDPR Article 32's "timely detection, reporting, and correction" mandate.
3. Procurement evaluation checklist: 6 key points for technical-legal co-validation
For technical evaluators and procurement officers, we highlight 6 verifiable metrics covering contracts to production:
- Data residency commitment: Whether contracts specify primary data center locations (e.g., Beijing Yizhuang IDC/Frankfurt AWS) with backup centers ≥1200km apart;
- PIA trigger threshold: Whether systems auto-generate PIA templates when daily new user data exceeds 50k entries or contains biometrics;
- Key management ownership: Whether HSM modules are client-managed or offer GM/T 0028-2014 compliant escrow services;
- Third-party audit frequency: Whether PenTest and SOC2 Type II reports are quarterly rather than annual summaries;
- Irreversible deletion: Whether storage medium overwrite proofs (per NIST SP 800-88 Rev.1) are provided within 3 business days post-wipe;
- Multilingual compliance: Whether Arabic sites embed GCC localization options (e.g., Saudi NCA-mandated DNS path controls).
A Zhejiang auto parts firm prioritized items 2,4,6: After integrating Saudi CDN, the system auto-mapped visitor IPs to NCA whitelists while replacing "car parts" with GCC-standard "automotive components" in SEO keyword libraries, avoiding regulatory risks from terminology variances.
4. Common misconceptions and risk mitigation
Misconception 1: "AI websites = black boxes." EasyStore provides full API documentation and data flow diagrams, enabling real-time tracking of inquiry data paths (e.g., form submission→SM4 encryption→P2 zone storage→email trigger→ERP sync). 2023 audit data shows 92% of evaluators completed first data chain verification within 2 hours.
Misconception 2: "GDPR conflicts with Chinese law." The frameworks complement—GDPR emphasizes data subject rights (e.g., right to be forgotten), while Chinese law focuses on processor liabilities (e.g., mandatory PIAs). EasyStore's dual-engine activates stricter log retention (730 days) and granular consent management (itemized checkboxes) in "EU-first" mode.
Misconception 3: "Multilingual sites increase risks." Contrarily, Arabic and Russian sites employ character set filters blocking UTF-8 injection attacks, with zero vulnerabilities detected in OWASP ZAP v4.5.2 scans.
For project managers and maintenance teams, the system provides a "security health dashboard," generating daily PDF reports with 17 metrics (e.g., unauthorized access attempts, key rotation completion, PIA expiration alerts), deliverable via email scheduling.
5. Conclusion: Making security a deterministic growth pillar
Data security boundaries aren't compliance endpoints but trust foundations. EasyStore's three-layer isolation translates abstract GDPR and PIPL clauses into verifiable, auditable technical realities. Whether Zhejiang exporters' multilingual sites or Middle East-facing automotive portals, the system delivers security baselines matching business radii.
Currently, this mechanism supports 2,300 clients passing EU CDD checks and China's Class 2 classified protection assessments. If you seek AI-powered, legally compliant cross-border website partners, contact EasyStore for customized data security whitepapers and PIA implementation roadmaps.
Related Articles
Related Products