I. Authoritative Definition, Strategic Core, and Risk Analysis of DDoS Protection for Foreign Trade Independent Websites
1. Authoritative Definition and Professional Elements of DDoS Protection for Foreign Trade Independent Websites
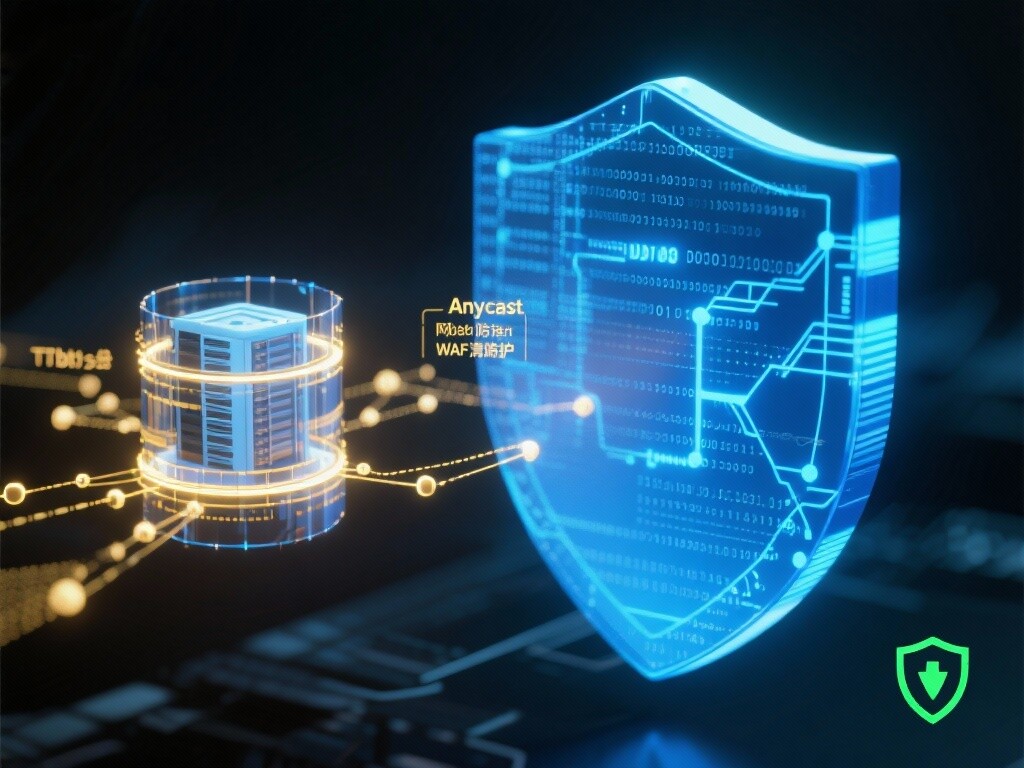
**DDoS Protection for Foreign Trade Independent Websites** refers to the comprehensive security service that utilizes **distributed network architecture, traffic scrubbing technology, and intelligent recognition algorithms** to conduct real-time monitoring, filtering, and mitigation of **Distributed Denial of Service (DDoS) attacks** targeting independent websites. Professional elements include: **high-capacity scrubbing (Tbit/s level), global Anycast network coverage, L7 application layer protection (CC attack defense), integrated Web Application Firewall (WAF), and SEO-friendly traffic filtering**.
2. The Three Irreplaceable Strategic Values of DDoS Protection for Independent Websites
Top-tier DDoS protection is the foundation for maintaining the competitiveness of independent websites:
- **Ensuring Business Continuity and Order Conversion:** Attacks causing website downtime directly result in the loss of **inquiries and orders**. Professional protection ensures the website **runs stably at high speed** even under attack, guaranteeing uninterrupted transaction processes.
- **Protecting SEO Rankings and Brand Reputation:** Prolonged website unavailability (4xx/5xx errors) prevents Google crawlers from accessing the site, leading to **significant drops in core keyword rankings**. Consistent stable operation is the basis for **Google E-E-A-T authority**.
- **Avoiding Data Leaks and Extortion Risks:** DDoS attacks often serve as **smokescreens for deeper intrusions**. A professional defense system comprehensively identifies threats, preventing leaks of sensitive customer and transaction data.
3. Common Risks and Historical Development of DDoS Attacks on Foreign Trade Independent Websites
Early stages (2000s): DDoS attacks primarily targeted **network layers (L3/L4)**, focusing on exhausting bandwidth. Mid-stage (2010s): Attacks shifted to **application layers (L7)**, such as CC attacks (targeting login/shopping cart resources). Modern era (2020s-present): Attacks have become **more complex and specialized**, featuring **“slow attacks,” “hybrid attacks,” and “competitive attacks”**, where competitors inject malicious traffic to exhaust server resources or disrupt SEO data, **exponentially increasing defense difficulty**.
II. The Five Core Technical Principles of DDoS Protection: Scrubbing, Recognition, and Coordination

Ensuring the defense system is effective without harming legitimate users involves the following underlying technical logic:
1. Anycast Network and Traffic Dispersion Scrubbing Principle
Principle: Using **Anycast routing technology**, attack traffic is dispersed to multiple global scrubbing centers, achieving **“dilution” of attack traffic**. Practice: During an attack, DNS directs requests to the nearest scrubbing node, **distributing Tbit-level attack pressure globally** for rapid mitigation.
2. L7 Application Layer (CC) Attack Defense Principle
Principle: Targets attacks that consume application layer resources (e.g., repeated login page refreshes). Practice: Employs **human-machine recognition (e.g., CAPTCHA), request rate limiting (Rate Limiting), and traffic fingerprinting** to accurately distinguish legitimate users from malicious requests, protecting core business systems.
3. Intelligent Traffic Fingerprinting and Behavioral Analysis Principle
Principle: Analyzes **HTTP headers, browser characteristics, IP addresses, geographic locations, and request frequencies** to establish traffic “fingerprints.” Practice: When traffic fingerprints **closely match known botnet or malicious crawler traits**, immediate blocking or verification is executed, achieving **millisecond-level precise defense**.
4. Web Application Firewall (WAF) and DDoS Coordination Principle
Principle: DDoS focuses on **ensuring network and application layer availability**; WAF focuses on **preventing application layer vulnerability attacks (e.g., SQL injection, XSS)**. Practice: Post-DDoS scrubbing, traffic undergoes **WAF security policy detection**, providing **dual protection** to prevent **penetrative attacks**.
5. SEO-Friendly Traffic Filtering and Whitelist Mechanism Principle
Principle: Prevents defense systems from misclassifying **search engine crawlers (e.g., Google, Bing) as malicious traffic**. Practice: Establishes **authoritative search engine crawler IP whitelists** and employs **granular traffic recognition strategies** to ensure crawler access, **avoiding SEO ranking losses due to over-filtering**.
III. The Four Core Technical Features and Applications of DDoS Protection for Foreign Trade Independent Websites
1. Technical Feature: Tbit/s-Level Global High-Capacity Scrubbing Capability
Feature: Capable of handling **terabit-per-second (Tbit/s) level traffic attacks**. Application: Effectively mitigates **large-scale reflective, amplified, and botnet attacks**, providing the highest-level capacity guarantee for foreign trade independent websites facing global threats.
2. Application Practice: Priority Protection for E-Commerce Payment and Login Pages
Application: For **order generation, payment confirmation, and user login**—key conversion paths—**highest-priority L7 application layer defense strategies** are deployed, ensuring smooth transactions even under attack, safeguarding conversion rates.
3. Application Practice: Malicious Crawler and Intellectual Property Protection
Application: Deploys **anti-crawler modules** to identify and block **machines maliciously scraping product prices, images, and content**, protecting the website’s **intellectual property and pricing system** from easy plagiarism by competitors.
4. Application Practice: Real-Time Security Alerts and Visualized Reporting
Application: Provides **24/7 real-time traffic monitoring and attack alerts**. Through **visualized security reports**, foreign trade businesses gain clear insights into **attack sources, types, and defense effectiveness**, aiding security decision-making.
IV. Professional DDoS Protection vs. Traditional Defense Models: Comparative Analysis and Industry Scenarios

1. Professional DDoS Protection vs. Traditional Defense Models: Comparative Analysis
2. Typical Industry Scenarios for DDoS Protection
Professional DDoS protection is a critical infrastructure for the following foreign trade independent websites:
- **Cross-border E-Commerce Platforms/Large Sellers:** High transaction volumes and intense competition make them frequent targets of malicious CC attacks.
- **Financial/Payment-Related Foreign Trade Service Sites:** Sensitive data and high extortion risks demand the highest security standards.
- **High-Tech/Patent Product Independent Websites:** Requires defense against competitors’ malicious scraping and website paralysis.
3. Certifications and Professional Standards for DDoS Protection Services
Criteria for evaluating high-quality DDoS protection services for foreign trade independent websites:
- **International Security Certifications:** Holds **ISO 27001, SOC 2**, and other global information security management certifications.
- **Scrubbing Capacity Reports:** Provides **Tbit/s-level** real-world attack scrubbing cases and reports.
- **SLA Availability Guarantee:** Commits to **99.99%+** website availability service level agreements (SLAs).
V. Deploy Top-Tier DDoS Protection Immediately—Let Your Foreign Trade Independent Website Operate Worry-Free with Uninterrupted Orders!
Don’t let a single cyber attack ruin months of marketing efforts! **Security is the primary productivity of foreign trade independent websites!** Our **DDoS Protection Solution for Foreign Trade Independent Websites** provides **global cloud scrubbing, intelligent WAF, and SEO-friendly filtering**. Schedule a **free “Independent Website Security Risk Assessment”** now to receive your customized security reinforcement plan!
Click to Get Your Free Security Reinforcement PlanFAQ
1. How Do DDoS Attacks Affect the SEO Rankings of Foreign Trade Independent Websites?
Answer: The impact is massive. Attacks render websites inaccessible, causing Google crawlers to receive **4xx or 5xx error codes**. Prolonged downtime leads Google to deem the site**unstable or offline**, potentially causing **significant drops in core keyword rankings or even delisting**. Professional DDoS protection ensures normal crawler access.
2. Do We Still Need Professional DDoS Protection If Our Servers Have Built-in Firewalls?
Answer: **Absolutely**. Server firewalls typically only defend against **small-scale, low-level L3/L4 attacks**. Against modern **Tbit/s-level massive traffic or L7 CC attacks**, server firewalls are breached before traffic reaches the server, **exhausting all server resources**.
3. How Does DDoS Protection Avoid False Positives Against Legitimate Users or Google Crawlers?
Answer: Through **intelligent traffic fingerprinting, behavioral pattern analysis, and professional SEO whitelist configurations**. The system identifies authoritative crawler IPs and behavioral traits, excluding them from defense strategies. For abnormal traffic, **human verification (e.g., CAPTCHA)** is used instead of direct blocking.
4. What Are the Hazards of L7 Application Layer (CC) Attacks on Foreign Trade Websites?
Answer: CC attacks simulate legitimate user requests (e.g., mass-refreshing product pages, searches, or cart additions), **exhausting server and database resources**, slowing sites to paralysis. This directly impacts **order generation and user experience**, making it a leading cause of business interruptions for foreign trade independent websites.

Customer Reviews
Mr. Chen, CEO of a Cross-Border E-Commerce Platform
“We were once targeted by malicious attacks from competitors, causing our website to crash for 4 hours and directly losing tens of thousands of dollars in orders. After deploying professional DDoS protection, we’ve endured several major attacks—**the site remains instantly accessible**, with attack traffic scrubbed at CDN nodes. **Business continuity is 100% guaranteed**, allowing us to focus entirely on promotions now.”
Manager Wu, High-Tech B2B Independent Site General Manager
"Our biggest concern was malicious crawlers scraping our technical parameters and pricing system. Their **WAF + DDoS collaborative defense** successfully blocked all malicious crawlers, **protecting our intellectual property rights**. More importantly, when subjected to CC attacks, **website performance remained unaffected**, ensuring a seamless experience for our high-end clients."
![Zero-code high-conversion website building: Practical templates for foreign trade independent websites Zero-code high-conversion website building: Practical templates for foreign trade independent websites]() Zero-code high-conversion website building: Practical templates for foreign trade independent websitesUse EasyShop's zero-code foreign trade independent website intelligent website building system to quickly achieve high-conversion foreign trade independent website building: Native integration of SSL certificates, DDoS protection, global CDN acceleration, combined with AI translation engines and AI ad diagnostics, and supports Google Ads optimization, Meta ad agency, and Yandex promotion. Apply for a demo now to quickly improve page speed and inquiry conversion.
Zero-code high-conversion website building: Practical templates for foreign trade independent websitesUse EasyShop's zero-code foreign trade independent website intelligent website building system to quickly achieve high-conversion foreign trade independent website building: Native integration of SSL certificates, DDoS protection, global CDN acceleration, combined with AI translation engines and AI ad diagnostics, and supports Google Ads optimization, Meta ad agency, and Yandex promotion. Apply for a demo now to quickly improve page speed and inquiry conversion.![Which SSL Certificate is the Safest for Foreign Trade Independent Websites? Expert Analysis Which SSL Certificate is the Safest for Foreign Trade Independent Websites? Expert Analysis]() Which SSL Certificate is the Safest for Foreign Trade Independent Websites? Expert AnalysisWhich SSL Certificate is the Safest for Foreign Trade Independent Websites? Experts Decipher Certificate Types, TLS Configuration, and Private Key Escrow, While Explaining Collaborative Solutions with Foreign Trade Independent Website DDoS Protection, Global CDN Acceleration, Smart Website Building Systems, and AI Advertising Diagnostics/Google Ads Optimization. Includes Cost, Compliance, and Implementation Recommendations. Click to Get Customized Solutions.
Which SSL Certificate is the Safest for Foreign Trade Independent Websites? Expert AnalysisWhich SSL Certificate is the Safest for Foreign Trade Independent Websites? Experts Decipher Certificate Types, TLS Configuration, and Private Key Escrow, While Explaining Collaborative Solutions with Foreign Trade Independent Website DDoS Protection, Global CDN Acceleration, Smart Website Building Systems, and AI Advertising Diagnostics/Google Ads Optimization. Includes Cost, Compliance, and Implementation Recommendations. Click to Get Customized Solutions.![How AI Ad Diagnostics Can Improve Conversion Rates for Foreign Trade Independent Websites? Case Analysis How AI Ad Diagnostics Can Improve Conversion Rates for Foreign Trade Independent Websites? Case Analysis]() How AI Ad Diagnostics Can Improve Conversion Rates for Foreign Trade Independent Websites? Case AnalysisThrough AI ad diagnostics for foreign trade independent websites, combined with SSL certificates, global CDN acceleration, and DDoS protection, we meticulously optimize Google Ads and Meta ad placements to achieve high conversion rates for independent websites and integrate with AI translation engines. Read case studies and practical solutions, apply for a free demo.
How AI Ad Diagnostics Can Improve Conversion Rates for Foreign Trade Independent Websites? Case AnalysisThrough AI ad diagnostics for foreign trade independent websites, combined with SSL certificates, global CDN acceleration, and DDoS protection, we meticulously optimize Google Ads and Meta ad placements to achieve high conversion rates for independent websites and integrate with AI translation engines. Read case studies and practical solutions, apply for a free demo.![Meta Advertising Agency for Independent Foreign Trade Websites: How to Choose a Reliable Partner? Meta Advertising Agency for Independent Foreign Trade Websites: How to Choose a Reliable Partner?]() Meta Advertising Agency for Independent Foreign Trade Websites: How to Choose a Reliable Partner?When selecting a Meta advertising agency for independent foreign trade websites, prioritize evaluating AI ad diagnostics, global CDN acceleration, DDoS protection and SSL certificate configuration for foreign trade sites, as well as high-conversion website capabilities. This article combines intelligent website systems, AI translation engines, Google Ads optimization, and Yandex promotion practices to provide actionable evaluation checklists and pilot solutions, helping you choose the right partner, quickly improve conversions, and obtain free diagnostics.
Meta Advertising Agency for Independent Foreign Trade Websites: How to Choose a Reliable Partner?When selecting a Meta advertising agency for independent foreign trade websites, prioritize evaluating AI ad diagnostics, global CDN acceleration, DDoS protection and SSL certificate configuration for foreign trade sites, as well as high-conversion website capabilities. This article combines intelligent website systems, AI translation engines, Google Ads optimization, and Yandex promotion practices to provide actionable evaluation checklists and pilot solutions, helping you choose the right partner, quickly improve conversions, and obtain free diagnostics.![AI Translation Engine Empowers Foreign Trade Independent Websites: Multilingual Operation at Lightning Speed AI Translation Engine Empowers Foreign Trade Independent Websites: Multilingual Operation at Lightning Speed]() AI Translation Engine Empowers Foreign Trade Independent Websites: Multilingual Operation at Lightning SpeedLeverage the AI Translation Engine for Foreign Trade Independent Websites alongside intelligent website-building systems, complemented by global CDN acceleration, SSL certificates, and DDoS protection for foreign trade sites, enabling rapid multilingual launch and enhanced conversion; built-in AI ad diagnostics assist in optimizing Google Ads, Meta advertising, and Yandex promotions, reducing costs and boosting sales—discover localized solutions now.
AI Translation Engine Empowers Foreign Trade Independent Websites: Multilingual Operation at Lightning SpeedLeverage the AI Translation Engine for Foreign Trade Independent Websites alongside intelligent website-building systems, complemented by global CDN acceleration, SSL certificates, and DDoS protection for foreign trade sites, enabling rapid multilingual launch and enhanced conversion; built-in AI ad diagnostics assist in optimizing Google Ads, Meta advertising, and Yandex promotions, reducing costs and boosting sales—discover localized solutions now.![Looking to expand into the Russian market? Yandex promotion strategies for foreign trade independent websites Looking to expand into the Russian market? Yandex promotion strategies for foreign trade independent websites]() Looking to expand into the Russian market? Yandex promotion strategies for foreign trade independent websitesLooking to expand into the Russian market? This article provides a practical guide to promoting foreign trade independent websites on Yandex, covering AI translation engines, SSL certificates, DDoS protection, global CDN acceleration, high-conversion website building, AI ad diagnostics, Meta ad agency services, Google Ads optimization, and intelligent website system selection. Click for free diagnostics and landing solutions.
Looking to expand into the Russian market? Yandex promotion strategies for foreign trade independent websitesLooking to expand into the Russian market? This article provides a practical guide to promoting foreign trade independent websites on Yandex, covering AI translation engines, SSL certificates, DDoS protection, global CDN acceleration, high-conversion website building, AI ad diagnostics, Meta ad agency services, Google Ads optimization, and intelligent website system selection. Click for free diagnostics and landing solutions.![Google Ads Optimization Secrets: Doubling ROI Solutions for Foreign Trade Independent Websites Google Ads Optimization Secrets: Doubling ROI Solutions for Foreign Trade Independent Websites]() Google Ads Optimization Secrets: Doubling ROI Solutions for Foreign Trade Independent WebsitesMaster Google Ads optimization and AI ad diagnostics, combined with SSL certificates, global CDN acceleration, and DDoS protection for foreign trade independent websites to create high-conversion landing pages and intelligent website systems; support AI translation engines, Yandex promotion, and Meta ad agency to achieve double ROI. Get a free diagnostic now to start improving overseas advertising performance!
Google Ads Optimization Secrets: Doubling ROI Solutions for Foreign Trade Independent WebsitesMaster Google Ads optimization and AI ad diagnostics, combined with SSL certificates, global CDN acceleration, and DDoS protection for foreign trade independent websites to create high-conversion landing pages and intelligent website systems; support AI translation engines, Yandex promotion, and Meta ad agency to achieve double ROI. Get a free diagnostic now to start improving overseas advertising performance!![How much can global CDN acceleration improve the speed of foreign trade independent websites? Test results How much can global CDN acceleration improve the speed of foreign trade independent websites? Test results]() How much can global CDN acceleration improve the speed of foreign trade independent websites? Test resultsActual tests show that global CDN acceleration for foreign trade independent websites can improve loading speed by an average of 30%~55%. Based on multi-node testing, this article evaluates the comprehensive impact of SSL certificates, DDoS protection, and CDN for foreign trade websites, providing practical procurement suggestions along with high-conversion website building, AI advertising diagnostics (including Google Ads optimization/Meta advertising agency), and optimization recommendations. Click to get free diagnostics and customized acceleration solutions.
How much can global CDN acceleration improve the speed of foreign trade independent websites? Test resultsActual tests show that global CDN acceleration for foreign trade independent websites can improve loading speed by an average of 30%~55%. Based on multi-node testing, this article evaluates the comprehensive impact of SSL certificates, DDoS protection, and CDN for foreign trade websites, providing practical procurement suggestions along with high-conversion website building, AI advertising diagnostics (including Google Ads optimization/Meta advertising agency), and optimization recommendations. Click to get free diagnostics and customized acceleration solutions.